

FaceCheck ID sits at a strange intersection of online safety, facial recognition, and open‑source intelligence. It is not a generic visual search tool, but a specialised engine that cares almost exclusively about one thing: faces. Understanding it properly requires looking beyond “upload a photo, get results” and unpacking what the system does, where it helps, and where it becomes genuinely risky.
FaceCheck ID is an AI‑powered reverse face search engine built to find where a specific face appears across publicly available web sources. Instead of matching whole images, it isolates the face from an uploaded picture, converts that face into a mathematical representation, and searches a large index of previously extracted faces for similar patterns.
The core purpose is identity‑oriented search. A single face image from a dating app, marketplace, messaging app, or social network can be used to discover:
● Other accounts where the same face appears under different names.
● Social profiles that confirm the person is real and consistent with their claimed story.
● Public records, discussions, or media in which that face has been featured.
This makes FaceCheck ID useful for scenarios such as avoiding catfishing, checking for stolen or stock profile photos, vetting strangers in high‑risk online interactions, and supporting OSINT and investigative work.
From a technical perspective, FaceCheck ID follows a fairly standard but carefully tuned facial recognition pipeline.
First, the system detects and isolates the face within the uploaded image. Background elements, text, and most visual clutter are ignored. The face is aligned so that key landmarks (eyes, nose, mouth) are positioned consistently, and basic normalisation is applied to mitigate differences in lighting and small rotations.
Second, the aligned face is passed through a deep neural network that produces an embedding: a high‑dimensional vector of numbers representing the underlying facial geometry and features. This embedding captures structural attributes like distances between landmarks, proportions of the jawline, nose shape, and other subtle patterns, rather than transient details such as hairstyle or makeup.
Third, that embedding is compared against a large database of embeddings derived from faces found in public web imagery. Efficient similarity search algorithms identify stored vectors that lie closest to the new one in this abstract space. These nearest neighbours are treated as candidate matches.
Finally, the system reconstructs a human‑readable results page: thumbnails of matched faces, grouped and ranked by similarity, accompanied by links to the websites where those faces appear. The user sees images and URLs, but what drives those results is purely geometric similarity in the embedding space.
It is crucial to understand that the system returns similarity, not legal identity. Matches represent faces that look highly likely to be the same person, according to the model and its training, but confirmation remains a human responsibility.
Operationally, FaceCheck ID is designed to be accessible to non‑technical users.
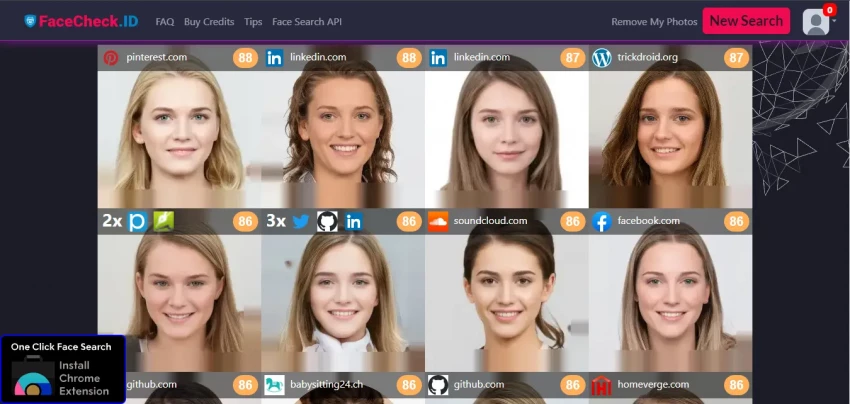
The typical workflow is straightforward: a user visits the site, uploads or drags in a face image (for example, a profile photo screenshot), waits a brief processing interval, and receives a results grid. Strong matches tend to appear higher in the grid, often with some form of confidence indication or implicit ranking.
Each candidate match usually includes multiple images of the same person collected from the associated site, plus a link to that source. Seeing the same face in different contexts and times helps the user confirm whether the match is genuine or coincidental. For example, a face appearing across several personal photos on a social profile is more convincing than a single, isolated image.
The interface avoids unnecessary complexity: there is no need to configure advanced settings to obtain useful output. This simplicity makes the tool effective for online daters, marketplace users, small business owners, and others who only need occasional checks, while still supporting more methodical use by journalists and OSINT practitioners.
In standard conditions, clear frontal photos, reasonable resolution, and relatively recent images, FaceCheck ID generally performs strongly. Under such conditions, the system is often able to surface convincing matches quickly, revealing whether a profile photo corresponds to a real, consistent online presence or to a repurposed identity.
However, performance is conditioned by image quality and context:
● Low‑resolution or heavily compressed images reduce the amount of usable facial detail.
● Extreme angles, partial occlusions (sunglasses, masks, hats), and strong filters can obscure key geometry.
● Large time gaps between the reference photo and indexed images can introduce differences due to aging, weight change, or other long‑term variations.
In these more challenging situations, the likelihood of both false negatives (missing the correct person) and false positives (surfacing someone who looks similar, but is not the same individual) rises. This is not specific to FaceCheck ID; it is inherent to face recognition as a probabilistic task.
For responsible use, results should be treated as leads that require interpretation and corroboration. The system is well suited to low‑stakes and medium‑stakes decisions such as choosing whether to proceed with an online interaction but is not appropriate as the sole basis for high‑impact actions like public accusations, formal background checks, or legal conclusions.
FaceCheck ID follows a credit‑based access model rather than offering unrestricted free use. Each face search consumes a certain number of credits. Users purchase credit bundles of varying sizes, from small packs suitable for occasional checks to larger packs for heavier use.
This has several implications:
● For individuals who run searches infrequently such as verifying a handful of online contacts per month, the credit model can be cost‑effective and avoids subscription lock‑in.
● For professionals or organisations that require high‑volume, systematic screening, costs can scale quickly, making it more suitable as a specialised tool rather than the central engine of an investigative workflow.
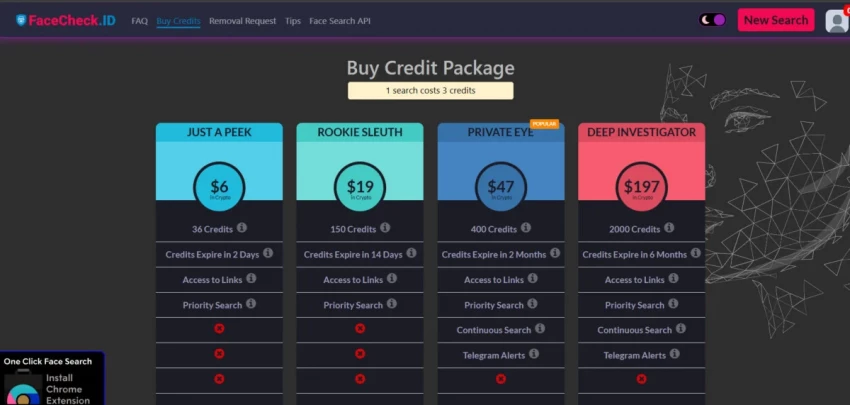
Overall, the pricing structure aligns well with ad‑hoc, protective use by individuals and small firms, but is less optimal for continuous, high‑throughput use compared with some enterprise‑grade or API‑centric alternatives.
The system fundamentally depends on large‑scale indexing of facial data from publicly accessible images. While those images are public in the sense that they are visible on the web, many individuals did not anticipate that their faces would be aggregated into a dedicated face search engine.
● Consent: Public visibility is not the same as informed consent for biometric indexing. Many people whose faces are searchable did not explicitly agree to this form of processing.
● Sensitivity of biometric data: Faces are biometric identifiers. In many jurisdictions, biometric data is considered a special or sensitive category, triggering stricter legal standards for collection, processing, and retention.
● Potential misuse: The same capabilities that enable self‑protection (detecting scams, verifying identities) can be misused for stalking, doxxing, harassment, or targeting vulnerable or pseudonymous individuals.
● Misidentification: Incorrect matches can connect someone to criminal records, controversial content, or reputationally damaging material they have no relation to, especially if users over‑trust similarity scores.
FaceCheck ID publishes guidance on responsible use, emphasising that results are informational, not definitive, and urging users not to employ the tool for harassment, discrimination, or illegal activities. However, technical guardrails only go so far. The risk profile of facial recognition is influenced as much by user behaviour and legal frameworks as by technical design.
From a privacy and ethics standpoint, FaceCheck ID is a powerful technology operating in a complex, evolving regulatory environment. It offers clear safety benefits while also contributing to a broader trend toward face‑as‑searchable‑identifier, which many privacy advocates find deeply concerning.
In practice, FaceCheck ID tends to be most useful in a few recurring scenarios.
1. Online dating and social platforms: A user can submit a dating profile photo to see whether the same face appears on other platforms under inconsistent names or in suspicious contexts. Discovering recycled images, multiple conflicting identities, or links to scam‑reporting forums can be a strong indicator that the profile is deceptive.
2. Marketplaces and remote work: Buyers, sellers, freelancers, and clients can perform quick checks on profile photos to reduce the risk of interacting with completely fabricated personas. If the face turns out to be a widely used stock photo or appears attached to unrelated identities, it signals a need for caution.
3. Parental and family safety: Guardians concerned about unknown adults contacting minors can use face search to identify whether that person has an established online presence or appears in worrying contexts. This is best combined with broader digital safety practices rather than used in isolation.
4. Journalism and OSINT: Investigators can use FaceCheck ID as one of several tools to link a face captured in a video, leak, or anonymous account to public appearances in other contexts. This can support identity verification, pattern mapping, and cross‑platform analysis, provided it is done under ethical and legal oversight.
Across all these workflows, the best practice is the same: treat FaceCheck ID as a signal generator, not as a final arbiter of truth.
From a technical and product standpoint, several strengths stand out:
● Focused functionality on face‑based search rather than broad image matching.
● Strong performance in favourable image conditions, with practical value in common real‑world use cases.
● Straightforward, accessible user interface that lowers the barrier to adoption.
● Credit‑based model that suits occasional or moderate use without requiring long‑term subscriptions.
The weaknesses are concentrated in areas where technology intersects with human behaviour and law:
● Potentially significant privacy and consent concerns due to large‑scale biometric indexing without explicit individual opt‑in.
● Risk of over‑reliance by users who may interpret probabilistic matches as certainty.
● Potential for serious harm from misidentification in high‑stakes contexts.
● Susceptibility to misuse for stalking, harassment, or targeting pseudonymous individuals.
As with most powerful tools, the net impact of FaceCheck ID is heavily dependent on context, governance, and user intent.
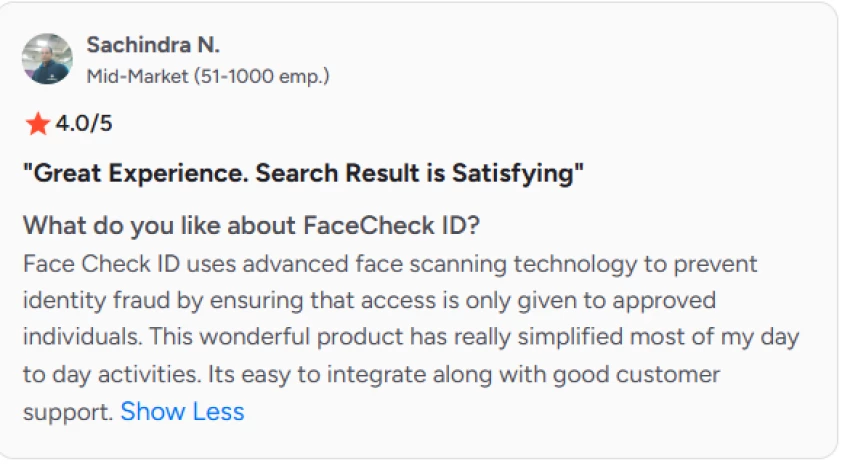
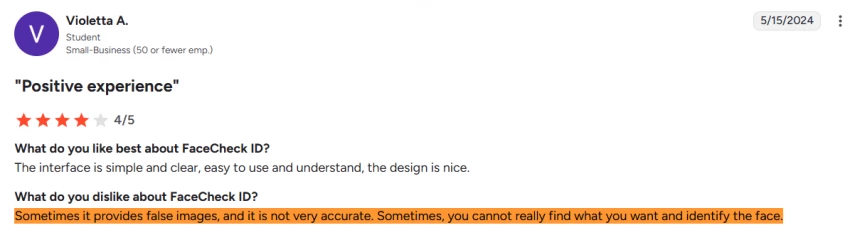
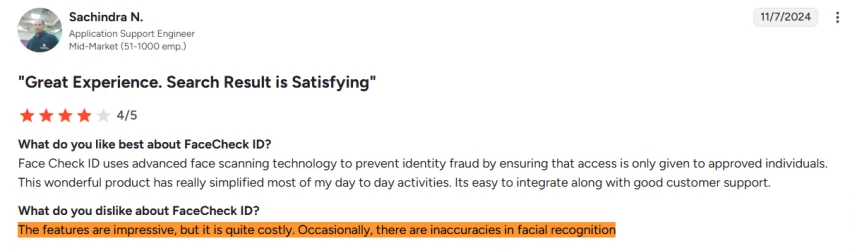
Users often describe FaceCheck ID as a tool that’s both powerful and limited. On the positive side, it’s easy to use, delivers fast results, and performs well with clear, front-facing photos. Many users appreciate its ability to find the same face across different sites, along with confidence scores that help judge match quality. Business users also highlight smooth API integration and responsive support.
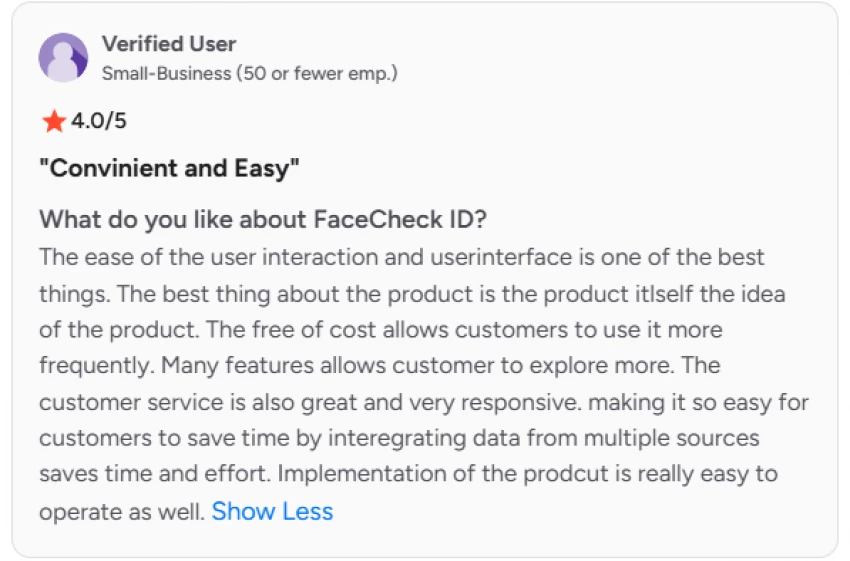
At the same time, reviewers consistently warn against over-reliance. FaceCheck ID is useful for spotting obvious mismatches or reused images, but it isn’t reliable enough to confirm someone’s identity on its own. It can fail when a person has little online presence or return similar-looking faces that may mislead users. As a result, experienced users recommend combining it with other tools like reverse image search and manual verification. Some also note concerns around pricing for frequent use and occasional performance or storage issues in app settings.
FaceCheck ID is best understood as a high‑leverage, high‑sensitivity instrument. It offers substantial practical value for personal safety and OSINT when used in low‑to‑medium‑stakes contexts, with results interpreted carefully and cross‑checked against additional information.
It is not appropriate to treat FaceCheck ID as a standalone background‑check solution, a definitive identity verification authority, or a tool for public accusation. In those roles, its probabilistic nature and exposure to bias and error pose unacceptable risks.
For individuals and small organisations, the most responsible positioning is as follows:
● A powerful second‑opinion tool to support decisions around trust in digital interactions.
● A starting point for further investigation, not the final word.
● A technology that should be used with explicit attention to privacy, consent, and proportionality.
FaceCheck ID illustrates both the promise and the discomfort of modern facial recognition. It increases the ability to detect deception and verify online identities, while simultaneously reinforcing a world where faces are persistent, searchable identifiers. Any adoption decision should acknowledge that duality and proceed with both the benefits and the societal implications clearly in view.
1. Can FaceCheck ID confirm identity?
FaceCheck ID cannot verify identity, it only shows visual similarities.
2. Can FaceCheck ID find social media profiles?
FaceCheck ID can sometimes link to social profiles if images are public.
3. Does FaceCheck ID store uploaded photos?
FaceCheck ID may process images temporarily, but users should check its privacy policy.
4. Is FaceCheck ID legal?
FaceCheck ID is legal for general use, but misuse can violate laws.
5. Can FaceCheck ID search private photos?
FaceCheck ID only scans publicly available images.
6. Does FaceCheck ID work on low-quality images?
FaceCheck ID performs poorly with blurry or cropped photos.
Discussion